Dealing with cookies
What are cookies?
- Online shopping sites such as Amazon use cookies to keep track of the items added to the “cart”
- Websites where you have configured yourself to remain logged in, such as Facebook, use authentication cookies to save the login details.
- Websites use cookies to remember user preferences. For example, Duckduckgo uses cookies to remember the viewing preferences of a webpage for the user.
However, cookies can also be used for malicious purposes. The degree of severity can range from tracking user data to target personalized ads, to stealing vital private information of the user.
There are many types of cookies based on their functions but a general user needs to know about two important categories: First-party and Third-party cookies. First party cookies are created by the website you are using. They are generally safe, as long as the website you are using is a reliable one. Third party cookies are created by websites other than the one the user is browsing. They allow third-parties to track data such as browsing history of the user.
Inspecting the cookie requests
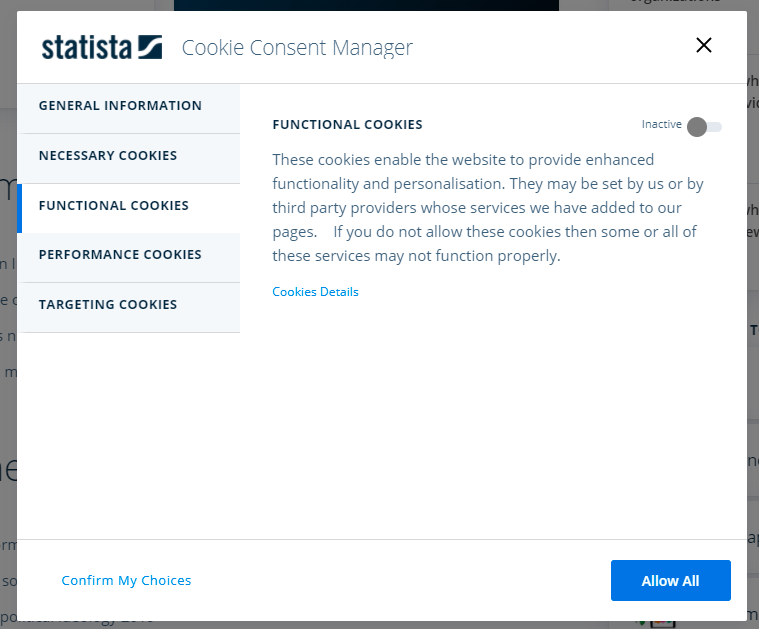
The above screenshot shows the default cookie preference for bbc.com. In this case the functional and performance cookies are on but can be made inactive by the user, The strictly necessary cookies at the top must be allowed to remain active or the website won’t function properly.
It’s always better to choose to manage the cookies instead of accepting all cookies; especially if you are visiting an unfamiliar website. Malicious cookies can be disguised as necessary cookies and saved in the device of unsuspecting users. Thus one needs to accept cookies with a grain of salt.
How to manage cookies on your device?
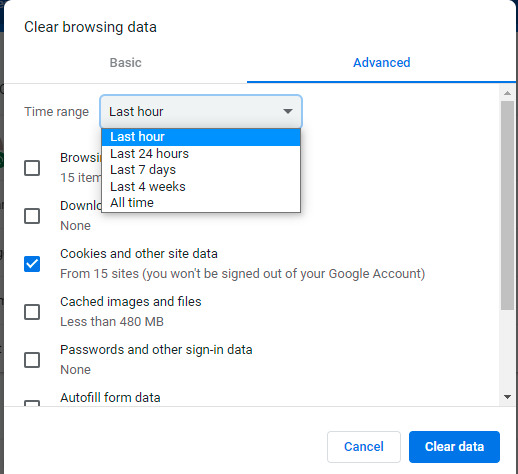
Choose the time range and delete the cookies so that your system remains free of any unwanted cookies you might have gathered while browsing. This won’t log you out of the websites you use frequently because those authentication cookies were created long ago and this action will delete cookies within an hour or a day, depending on the option you choose.
You can also configure your browser to block third-party cookies, and to delete the recently added cookies. The instructions provided here are for google chrome browser but it’s similar with other browsers too.
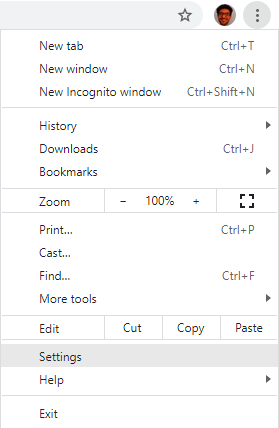
Go to settings.
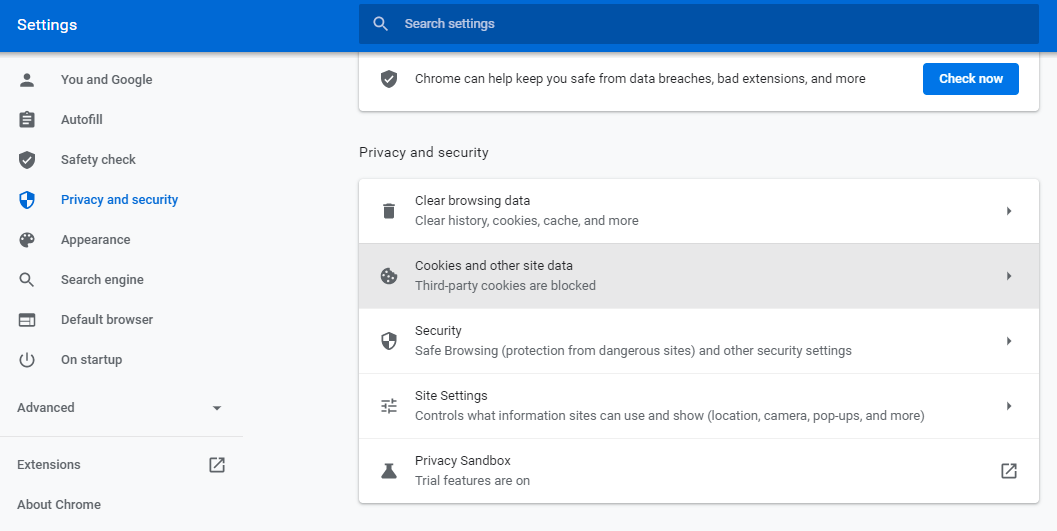
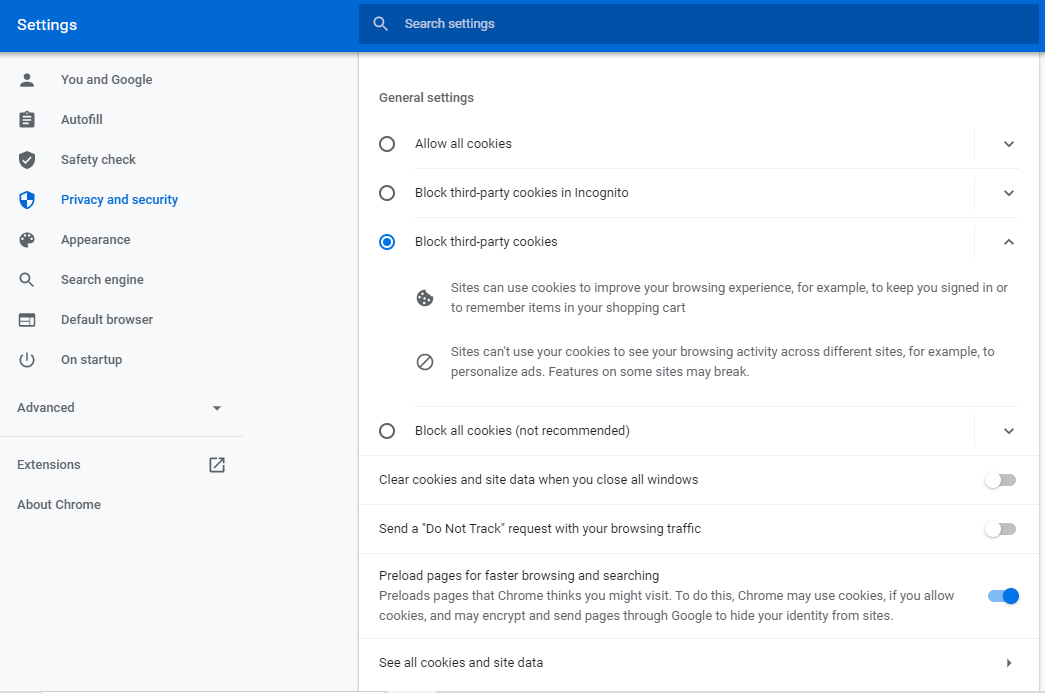
More options appear as shown above. Select the block third-party cookies options. This might disable some features such as downloading materials from google drive. You’ll have to enable the cookies again if you face such problems. If you want to have a look at the cookies stored by various sites in your de
Knowing the reality of things always helps us make better decisions. This blog has highlighted one concern about the digital world. To learn about more things to keep an eye on, refer to our blog on the dangers of communication and information sharing.